What are the types of Hackers?
by : Vyshu <vaishnavu c v > 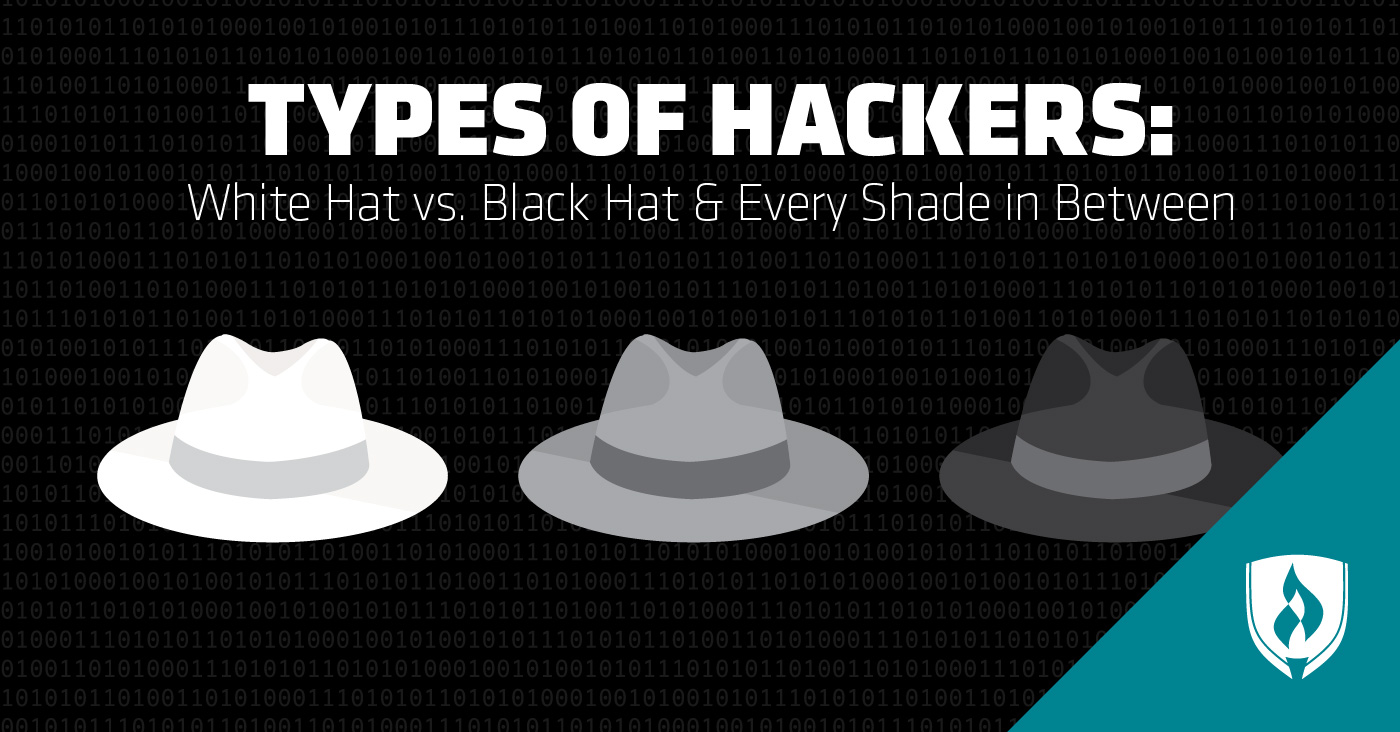
Hackers can be segregated according to their intent.
White Hat Hacker
 It
is another name for an Ethical Hacker. They hack into a system with
prior permission to find out vulnerabilities so that they can be fixed
before a person with malicious intent finds them.
It
is another name for an Ethical Hacker. They hack into a system with
prior permission to find out vulnerabilities so that they can be fixed
before a person with malicious intent finds them.
Black Hat Hacker
 They
are also known as crackers, who hack in order to gain unauthorized
access to a system & harm its operations or steal sensitive
information. It’s always illegal because of its malicious intent which
includes stealing corporate data, violating privacy, damaging the system
etc.
They
are also known as crackers, who hack in order to gain unauthorized
access to a system & harm its operations or steal sensitive
information. It’s always illegal because of its malicious intent which
includes stealing corporate data, violating privacy, damaging the system
etc.
Grey Hat Hacker
 They
are a blend of both black hat and white hat hackers. They mostly hack
for fun and exploit a security weakness in a computer system or network
without the owner’s permission or knowledge. Their intent is to bring
the weakness to the attention of the owners & earning some bug
bounty.
They
are a blend of both black hat and white hat hackers. They mostly hack
for fun and exploit a security weakness in a computer system or network
without the owner’s permission or knowledge. Their intent is to bring
the weakness to the attention of the owners & earning some bug
bounty.
Suicide Hacker
 A
suicide hacker is a person who works with the intent to bring down
major corporations and infrastructure. These kinds of hackers are not
scared of the consequences of their actions as they mostly work with a
vengeance in their mind. These people are also known as hacktivists.
A
suicide hacker is a person who works with the intent to bring down
major corporations and infrastructure. These kinds of hackers are not
scared of the consequences of their actions as they mostly work with a
vengeance in their mind. These people are also known as hacktivists.
What are the different types of hacking?
Now that we have discussed the various types of Hackers, let’s go over the different types of hacking. We can segregate hacking into different types depending on what the hacker is trying to achieve.
Website Hacking
 Hacking
a website means taking unauthorized control over a web server and its
associated software such as databases and other interfaces.
Hacking
a website means taking unauthorized control over a web server and its
associated software such as databases and other interfaces.
Network Hacking

Hacking a network means gathering information about a network by using tools like Telnet, NS lookup, Ping, Tracert, Netstat, etc. with the intent to harm the network system and hamper its operation.
Email Hacking
 This
includes gaining unauthorized access to an Email account and using it
without taking the consent of its owner for sending out spam links,
third-party threats, and other such harmful activities.
This
includes gaining unauthorized access to an Email account and using it
without taking the consent of its owner for sending out spam links,
third-party threats, and other such harmful activities.
Password Hacking
 This is the process of recovering secret passwords from data that has been stored in or transmitted by a computer system.
This is the process of recovering secret passwords from data that has been stored in or transmitted by a computer system.
Computer Hacking
 This
is the process of stealing computer ID and password by applying hacking
methods and getting unauthorized access to a computer system.
This
is the process of stealing computer ID and password by applying hacking
methods and getting unauthorized access to a computer system.
Comments
Post a Comment